Audit logs
DoiT Cloud Intelligence provides audit logs to help you respond to security events, internal investigations, and compliance obligations. Audit logs are a chronological record of events across all areas of DoiT Cloud Intelligence, capturing the who, what, when, where, and why of every operation, providing total visibility into the actions taken within your accounts.
Audit logs are retained indefinitely. The audit data trail remains accessible within DoiT Cloud Intelligence as long as your organization remains a customer.
Required permissions
To access audit logs, your DoiT account must have the Admin role.
Access audit logs
To access audit logs, sign in to the DoiT console, select the gear icon () from the top navigation bar, and select Audit logs.
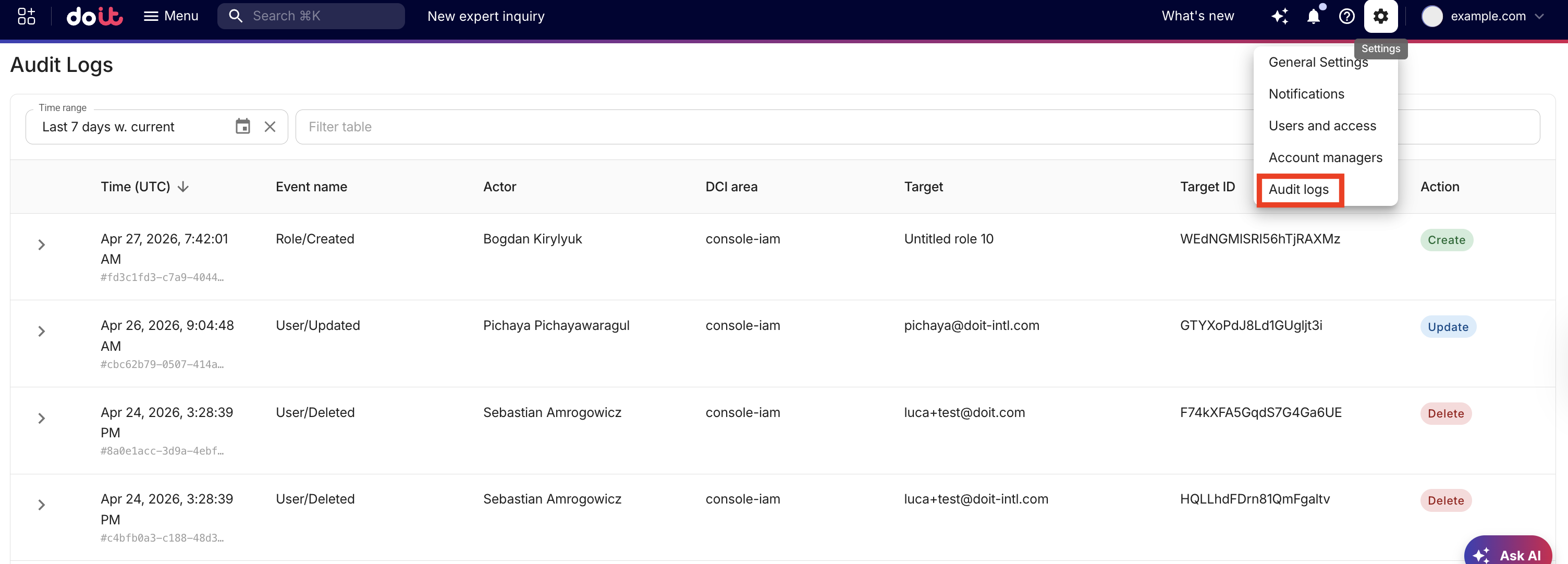
By default, the audit log displays the events from the last 7 days, sorted by time from newest to oldest. The following information is displayed for each event.
| Field | Description |
|---|---|
| Time | The date and time the action occurred. The timestamp is in ISO 8601 format (UTC). Hover over the event ID to view the full identifier. Use the Copy icon to copy it to your clipboard. |
| Event name | A descriptive label for the specific event that occurred, such as Cloud Analytics/Report/Create. Use this field to differentiate between event types that occur with the same area and share the same action. |
| Actor | The actor represents the entity that performed the action. This displays a username for individual actions (as defined in DoiT Cloud Intelligence), or DCI for system-level actions performed by DoiT Cloud Intelligence. |
| DCI Area | The area of DoiT Cloud Intelligence where the event occurred, for example, Alerts, Anomalies, CloudFlow, Cloud Diagrams, and so on. |
| Target | The human-readable resource name where the event took place. |
| Target ID | The unique identifier of the target resource. Together with Target, it identifies exactly which resource was changed (for example, a specific budget, alert, or dashboard). You can filter by Target ID to see all events for that resource. |
| Action | The action that occurred. Values are either Create, Update, or Delete. |
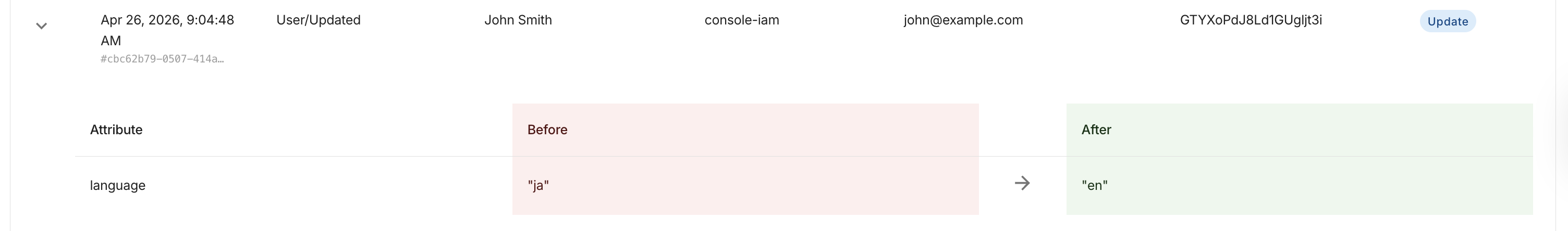
View audit event details
To view an audit event's details, expand the event whose details you want to view. The event details are generated in a comparison window that displays a before and after snapshot, allowing you to see the exact changes made during the event.
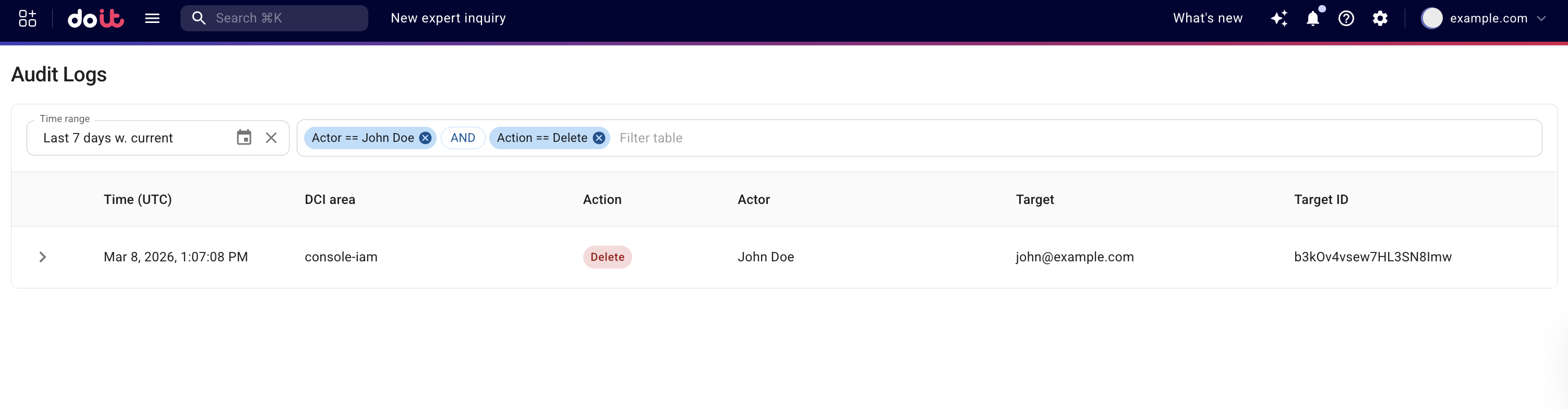
Filter audit logs
Instead of searching through audit logs, you can use filters, enabling you to quickly and easily focus on the events you are interested in. You can filter audit logs:
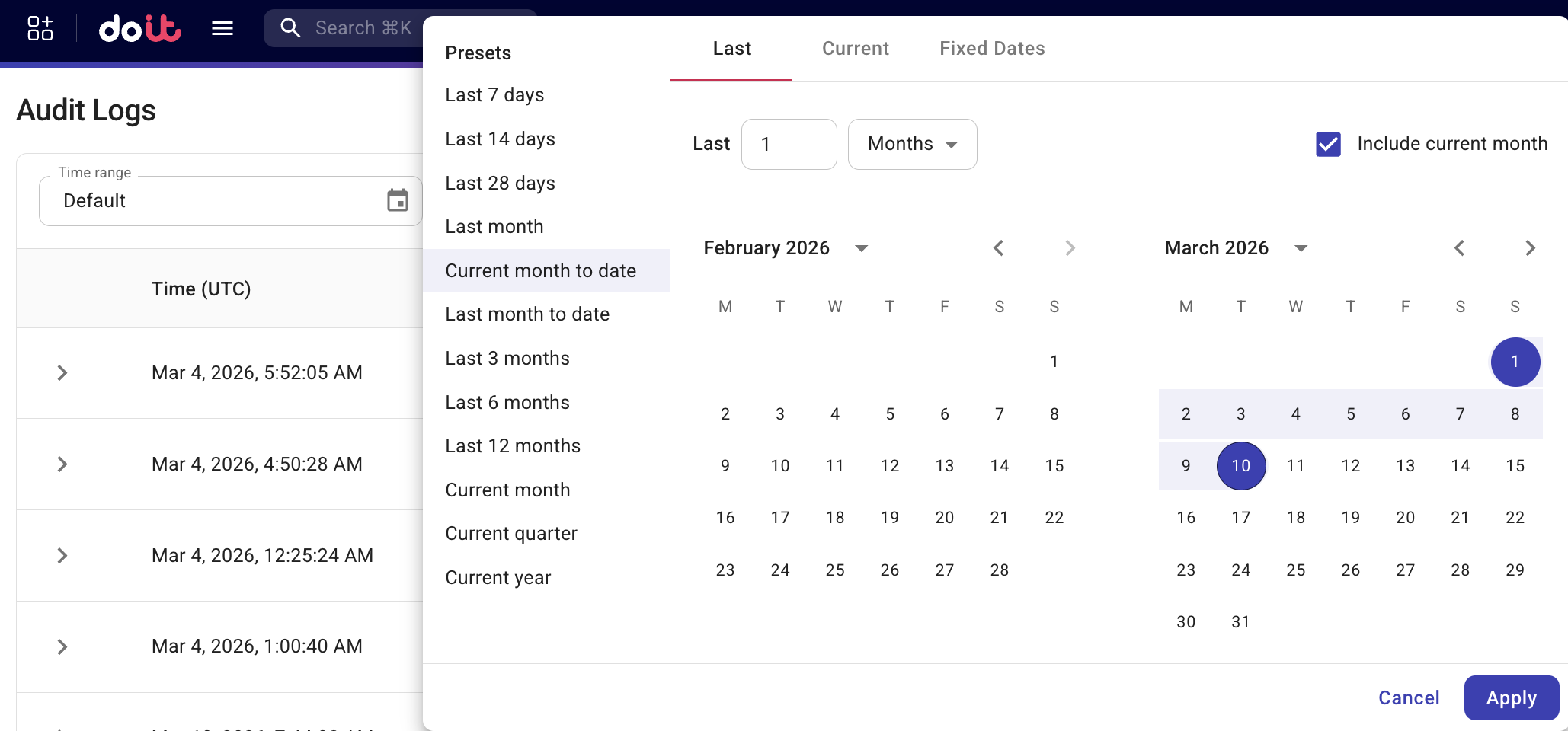
- Based on a time range. You can choose a predefined range or specify a custom one. Setting the time range to
Defaultrestores the default setting.
-
By fields: event name, DCI area, action, actor, target, and target ID. You can use regular expressions for pattern-based searches across all fields. Filtering by target ID is useful to trace all events for a specific resource.
-
Add individual events to a filter to build a custom search based on specific event criteria. Hover over the event and select + to add the event to the filter.
For example, you might want to see all Delete actions performed by a specific actor over the last 7 days.